Monitoring unauthorized internet accesses through a 'honeypot' system - Marchese - 2011 - International Journal of Communication Systems - Wiley Online Library

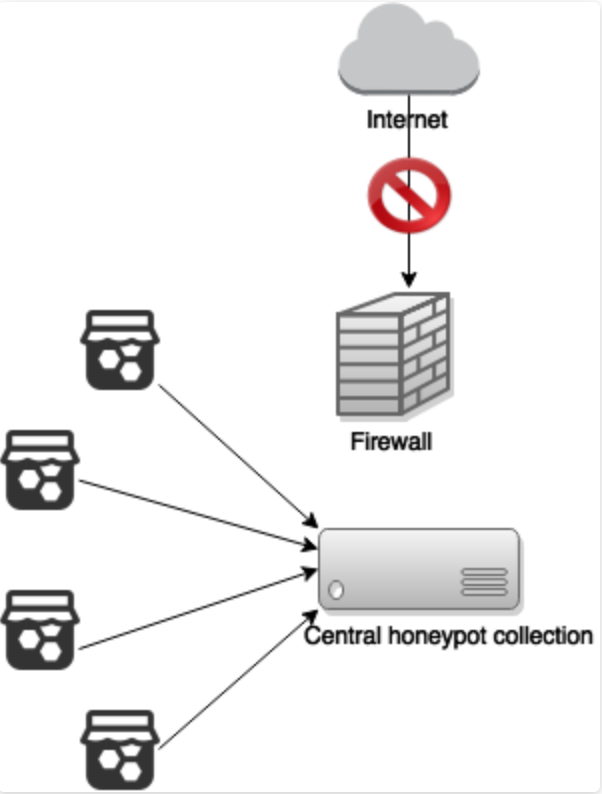
A Honey Net, Big Data and RNN Architecture for Automatic Security Monitoring of Information System | SpringerLink






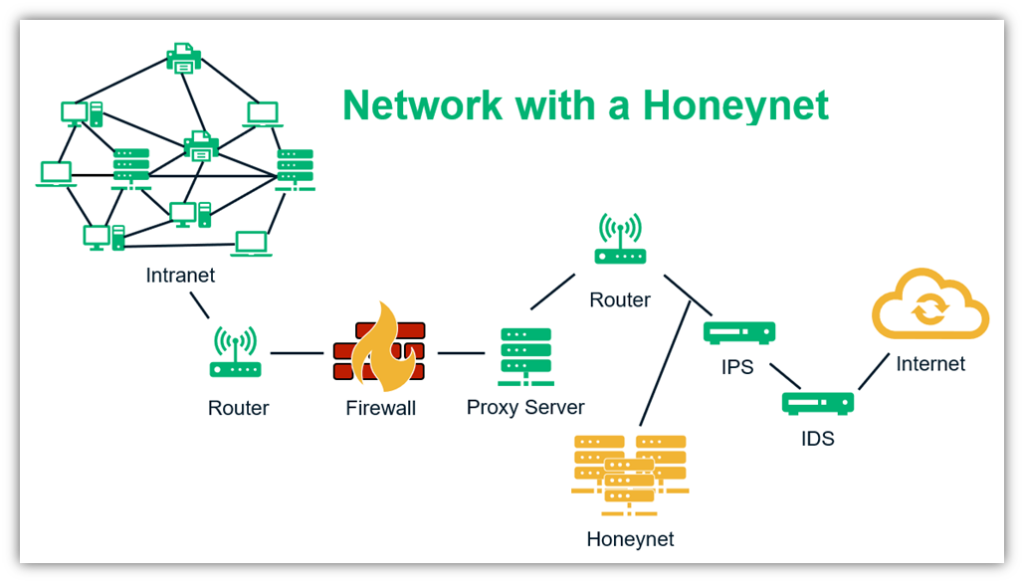
![PDF] Honeypot in network security: a survey | Semantic Scholar PDF] Honeypot in network security: a survey | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/e7f1c0185e86318b4330eea5385f0cfa3f6ad0e1/3-Figure1-1.png)

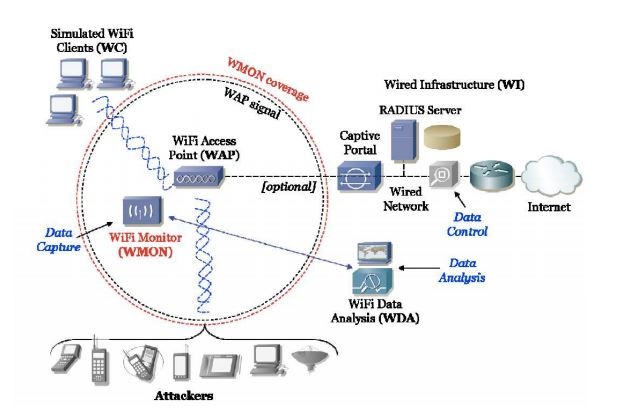




![Hybrid client honeypot architecture [23] | Download Scientific Diagram Hybrid client honeypot architecture [23] | Download Scientific Diagram](https://www.researchgate.net/profile/Peter-Komisarczuk/publication/202141505/figure/fig2/AS:667681795624961@1536199153132/Hybrid-client-honeypot-architecture-23.png)